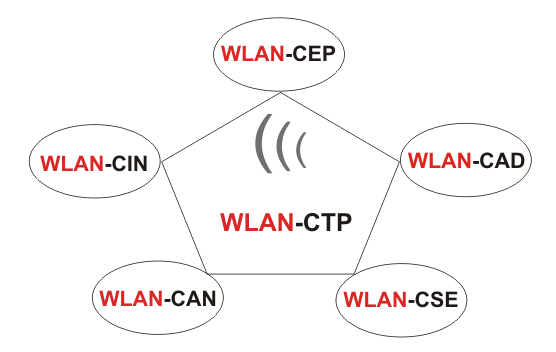
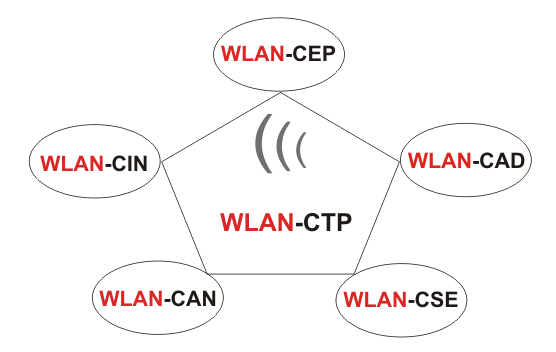
Wireless LAN Certified Training Program (WLAN-CTP)
A Closer Look at RF Interference and
Spectrum Analysis - Part 1
Jesse
Frankel, AirMagnet Product Marketing Manager at Fluke Networks
RF
interference has become a common source of disruption amongst enterprise WLANs.
In order to improve IT support effectiveness and reduce user productivity loss
and frustrations, spectrum analysis functionality is being increasingly deployed
in WIPS sensors and WLAN APs.
In
this first post, lets go over some RF interference and spectrum analysis
basics. Before we dive into the deeper discussion of deployment models, we need
to first establish what RF interference is and why enterprises need spectrum
analysis.
What
is RF interference? Here are some technical definitions of the key pieces, as
they pertain to our discussion:
RF Interference
RF transmitting devices that do not use the 802.11 PHY or MAC components, but
transmit in the same frequency bands used by standard 802.11 (Wi-Fi) data
communications devices and APs. Lets refer to this type of interference as
RFI (RF Interference). RFIs can include microwave ovens, cordless phones,
Bluetooth devices and more. (Rogue APs, neighboring APs and other Wi-Fi devices
not part of the users authorized network are not considered interference in
this sense.)
RFI Classification
As most IT professionals are not well versed in the technical aspects of
spectrum analysis, most embedded spectrum analysis-enabled sensors and APs have
some capability to classify the analysis data. The classification will typically
include the type of interfering source device, which is determined via some
pattern matching processes, and may also include information about power level,
time of onset, RF duty cycle, Wi-Fi channels affected and other similar metrics.
This information can greatly simplify the IT support problem diagnosis and
remediation job. As with any other intelligent detection technology, RFI
classification should be quick, accurate (only trigger on real
RFI sources) and precise (give the correct matching information elements).
And
what about spectrum analysis?
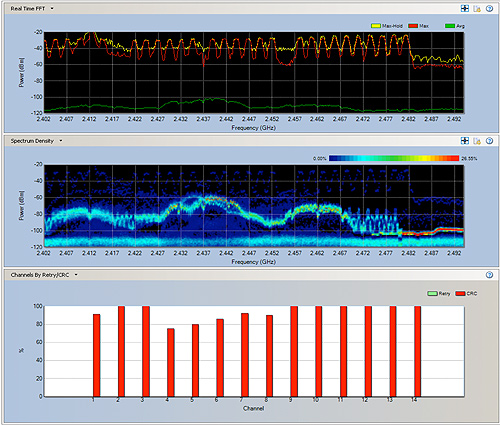
Spectrum Analysis (SA) Capability Types
Frequency domain (FFT) processing is a universal feature of SA solutions (sensor
or AP-based), providing analysis of the spectral power levels of the RF energy
present in the received signal. Time domain processing provides additional
temporal information on characteristics of the received signal, such as accurate
pulse width and pulse shape measurement. There are two basic implementation
types found in embedded SA-enabled sensors and AP one where the LAN chipset
performs the FFT analysis and an embedded or separate network processor does the
classification analysis, and a second type where a fully dedicated SA processing
module performs both the frequency and time domain signal analysis, with the
classification analysis performed with a dedicated processor.
SA Radio and Processing Specifications
SA radios and systems can carry a large collection of detailed specifications.
Compared to lab bench instruments-grade spectrum analyzers, which may have many
relevant specification items, there are only a few which are relevant for the
class of embedded SA processors were considering. Some of these include:
resolution bandwidth (RBW), sensitivity, dynamic range, sampling rate or
sampling period. RBW specifies the analyzers ability to resolve signal
components spaced closely in the frequency domain.
Why
do enterprises choose to deploy SA-capable WIPS sensors? Weve found there are
two main decision drivers. First: previous pain. These are cases where IT
engineering and support have experienced severe WLAN problems, which have defied
standard Wi-Fi analysis techniques and have, perhaps, persisted stubbornly.
Ultimately it was determined that the actual root cause of these issues was
related to RFI sources impacting WLAN operation. In these cases, where prior
pains were evident, there is awareness of the benefits of SA capability to
improve support productivity and limit business network downtime.
The
second decision driver, weve found, is the need for future protection. Maybe
you havent experience a problem yet, but you are acutely aware that that
could change any minute. With the proliferation of Wi-Fi and other wireless
technology in the enterprise, both from IT deployments and employees personal
devices, there is a high likelihood that incidents of RFI impacting business
Wi-Fi networks will continue to increase. In order to be well positioned to
quickly detect and remediate this class of WLAN problems, deployment of
SA-enabled WIPS sensors, in advance of issues, provides the necessary readiness.
A Closer Look at RF Interference and
Spectrum Analysis - Part 2
Author
- Jesse Frankel, AirMagnet Product Marketing Manager at Fluke Networks
What
are the various approaches for deployment?
Partial deployment/trouble area only:
This
mode comes into affect in cases where there are certain critical areas where
WLAN problems occur most often, or users are most sensitive to even short
network interruptions (i.e., executive boardrooms, auditoriums, IT operations,
help desk and lab areas).
Full
deployment: In this mode, SA-enabled WIPS sensors are deployed wall-to-wall in
all key areas to provide complete RFI detection and analysis capability.
Headquarters and remote sites are often prioritized highest for this deployment.
Permanent vs. temporary deployment:
Sensors
are most commonly deployed in a permanent installation mode. Other times, it can
be effective to temporarily deploy SA-enabled sensors on an as-needed basis to
areas that appear to have WLAN symptoms that point to RFI as a potential root
cause. This can be a very efficient starting point for the use of SA-enabled
sensor technology. Sensors can be temporarily deployed to a trouble area for
days or weeks until the RFI source is confirmed (or some other root cause is
determined).
Coupling with AP infrastructure deployment:
There
is a wide variation in this area, so there is no real typical case. Some sensor
decisions are driven by AP upgrade or expansion projects, while others are
completely decoupled and driven by support improvement or security monitoring
projects.
Considering
an SA monitoring system for your enterprise? When considering the suitability of
SA monitoring systems and comparing different products, its important to know
the various technical aspects that are key in the decision-making process:
Classification accuracy: Time
domain analysis provides large improvements in RFI classification accuracy. Many
interferers have pulse durations that are in 10s of milliseconds. These may be
estimated from FFT data alone, however, there are a number of cases where the
difference between pulse duration across interferer classes is only a few
milliseconds. This makes proper classification by only the FFT data very
difficult. Examples of this include computer mice, zigbee, game controllers and
bluetooth interferers, all of which look extremely similar in the frequency
domain, but are clearly differentiated based on pulse characteristics.
There
are always new RFI sources being introduced into the enterprise environment.
This means that the most capable processing approach will increase the
likelihood of classification, and that the system architectures that can most
quickly update and expand the classifier signature database will be the most
effective. Classification performance includes how quickly and accurately an RFI
is classified. Part of the accuracy is the ability to differentiate between
signals with similar characteristics (such as a wideband jammer or a microwave
oven). In these cases, the addition of time domain processing means being able
to tell a malicious attack from unintentional interference from a kitchen
appliance. This differentiation is vital to initiating the proper remediation
approach.
Remote real-time analysis, forensic capture:
Along
with RFI classification, having the ability to easily view the real-time SA
interference across the network to a remote site is valuable for the diagnostic
and remediation steps. There may be multiple RFI sources to deal with, or
sources that exhibit only periodic transmissions, where after being alerted by
an automated mechanism to the problem, further investigation is needed. Also,
systems that can capture forensic SA data at the time of the RFI classification,
and store these informational elements for future analysis, add a further
important capability (i.e., an RFI that only comes on at night when no staff is
present could be fully diagnosed with stored capture information the next
morning).
Specification
comparisons: Unlike lab instrument grade analyzers, the vendors of the embedded
SA processor modules utilized in IT equipment do not typically quote any
standard set of specifications. Some provide little to no specifications, while
others quote various items in nonstandard format or convention. This means it is
generally difficult to evaluate the real capabilities of the various solutions
by comparing specifications.
System
deployment flexibility: Depending on plans for WLAN expansion and refresh cycles,
the desire to add SA monitoring may or may not coincide with deployment plans
for other infrastructures. In terms of cost efficiency, if all the timing lines
up, it may be beneficial to deploy SA monitoring concurrent with other WLAN
infrastructure. However, we find that often IT may want to start off with a
small system which can be used in temporary or permanent deployment mode in
order to understand its full benefits. An overlay sensor approach also adds
significant advantages in many cases, including the ability to quickly and
easily update and add classification signatures and perform the SA processing
without impacting the performance of the AP itself.
Clearly,
there are many factors that go into evaluating and selecting what type of
spectrum analysis deployment is right for you and your enterprise.
A
Closer Look at RF Interference and Spectrum Analysis - Part 3
Author - Jesse Frankel,
AirMagnet Product Marketing Manager at Fluke Networks
So
far, we've taken a deep dive into basic RF interference and spectrum analysis
definitions, decision drivers, deployment models and technical comparisons. With
this final post in the series we will examine the technical and deployment
trends we see in the field.
As
the use of all kinds of wireless technology continues to grow in the enterprise,
some interesting technical trends have emerged:
More
virulent RFI sources Employees, visitors and IT staff are using more
wireless enabled devices (typically using 2.4 GHz band), causing more potential
headaches for Wi-Fi users and IT support staff. Many of the troublesome devices
use a point-point RF link and many energize the link at or near 100% duty cycle
meaning just one such gadget can have a strong impact on a fairly large
physical area. We have come across two noteworthy gadgets in real customer
scenarios: audio headsets and wireless backup cameras.
Audio
Headsets: Audio headsets that connect to laptops via USB dongle receiver are
often used by employees in an IT support area. The transmitter for these devices
runs at almost 100% duty cycle, even when the headset itself is not turned on.
Even if a new source type like this is classified as a generic interferer,
understanding the complete spectral landscape is very valuable to making an
accurate diagnosis and planning the best course for remediation.
Wireless
backup cameras: Small video cameras with point-point wireless links are not new
to the world of Wi-Fi RFI. However, a new twist is that various types are
finding their way into more places. A recent discovery was made of a car
bumper-mounted backup-viewing camera with a wireless link to a display device.
The wireless link for this device runs at 100% duty cycle and transmits in two
bands. The RFI source can completely knock out Wi-Fi communication across the
channel, and the high duty cycle and high power in close proximity to WLAN
network infrastructure can also cause other side effects, likely due to
desensitization and signal processing slow down in the presence of this RFI
source.
Slow
migration from 2.4 GHz WLAN use Although 802.11n infrastructure is expanding
in the enterprise space, the migration away from the use of b/g/n in the 2.4 GHz
space continues to be very slow. While some enterprise IT groups have specific
plans in place to migrate business users to a/n on the 5 GHz band, most do not.
The reason for this is there are some competing factors at play, as most mobile
devices (including smart phones) only support 2.4 GHz, as well as the possible
slowing of laptop replacement over the last two years. The increased use of
voice-over-WLAN and other high data intensity applications, like video streaming,
also means that RFI impact, even from sources with intermittent or fairly low
duty cycles, will become even more of a nuisance. This means that the impact of
RFI on business uses of WLAN will continue to worsen, and that IT support will
find it increasingly difficult to resolve WLAN issues without an SA-capable
monitoring solution in place.
Increasing
understanding of spectrum management strategy Many important users and
devices now depend on reliable WLAN services. Because of this, many IT groups
understand the importance of developing a comprehensive spectrum monitoring and
management strategy. Healthcare institutions were the first to recognize the
importance of setting official policies for the use and monitoring of relevant
spectrum in and around their premises in order to protect the reliability of
mission critical applications, as well as minimizing the chances of RFI sources
and neighboring devices having a negative impact. Instituting these kinds of
policies can impact overall IT cost, often because costs can increase due to the
hidden effects of unseen RFI and other unauthorized devices that may be in use.
Without spectrum monitoring capabilities, there is no way to understand the
risks that may be present.
Although
healthcare has provided most of the momentum for SA-enabled deployments, there
is significant motion in the enterprise sector, with an increasing interest from
traditional carpeted office enterprises for SA deployment.
What
are the trends for enterprise deployment?
General
interest and demand level The first trend we see is in general interest and
demand levels. We see a marked increase in opportunities for full-time,
SA-enabled sensor deployments from traditional enterprises such as financial
services, insurance and manufacturing companies. As the added cost of the SA
capability has decreased and the rate of WLAN problems due to RFI increases,
more IT engineering and support groups are recognizing the value. The decision
drivers fall about equally into the previous pain and future protection
categories.
SA-enabled
sensor ration The second trend is the SA-enabled sensor ratio. In 2010,
about 40% of our sensor shipments were SA-enabled. This is a huge jumpover
300% from the year before. Most of the growth was driven by healthcare related
applications, but we have some very significant new projects expected soon from
the traditional enterprise space that will push the ratio even higher.
AirMagnet
Survey and Planner Integrate with Cisco WCS to Streamline Wireless Network
Planning and Management
Author - Chris Roeckl, vice president of marketing at AirMagnet
Exciting
news for all of our Cisco customers. Today we're announcing that AirMagnet
Survey and AirMagnet
Planner now integrate with the Cisco
Wireless Control System (WCS). This integration dramatically increases
operational efficiencies for both AirMagnet and Cisco WCS customers by
eliminating the need to repeat wireless planning and site survey tasks commonly
associated with deployment and ongoing management of a WLAN network.
We
(AirMagnet) have a lot of Cisco customers that utilize our industry-leading
wireless planning and site survey technology. However, to get the best of both
worlds, they have to repeat many of the same mapping and survey activities, both
during the planning and deployment phase, as well as when they set up their
ongoing network management tools. This new integration eliminates the need to
repeat many of those activities and allows an IT administrator to easily import
all the planning and survey data right into the Cisco WCS system.
One
of our fantastic customers, Dennis Holmes, Mobility Practice Manager at
Internetworking Engineering, commented, "AirMagnet Survey and Planner are
the industry's de facto solutions for WLAN site surveys and planning. These new
integrations will allow our organization to easily leverage these powerful tools
for upgrading or deploying Wi-Fi networks utilizing Cisco WCS for ongoing
management. Currently for customers with Cisco WCS, we use AirMagnet tools for
AP deployment, calibration and other substantial data gathering activities, then
we have to repeat this exercise with Cisco's set of tools. This new integration
will be the best of both worlds, eliminating the extra steps while still
allowing us to use best-of-breed tools."
Users
can take advantage of the planning capabilities of the industry-leading planning
tool, AirMagnet Planner, and create and export planner projects directly to
Cisco WCS. This saves users time and resources needed in setting up of maps, AP
placement locations and other WLAN deployment modeling activities by eliminating
the need to repeat these tasks within Cisco WCS.
AirMagnet
Survey is the industry's only WLAN site survey tool that allows exporting of
real-world survey data to Cisco WCS. This is critical for not only calibrating
Cisco's built-in Planner modeling capabilities, but also for specialized
applications. For example, location services that mandates a calibration site
survey for maximizing location accuracy for WLAN clients or tags, and VoWLAN
services that recommends the use of site surveys to validate real-world data
versus the predictive capabilities of the infrastructure.
Furthermore,
Cisco recommends site surveys for voice deployments. The Cisco Voice over WLAN
Design Guide states, "Despite the effort and care applied at the front end
of the system the only true measure of their quality and the prediction system
is to measure the output. The means of output measurement is a site survey...
site survey tools such as AirMagnet provide a much richer interface view of the
data collected."
For
more information on AirMagnet Survey and Planner, please visit http://www.airmagnet.com/products/
New
integration capabilities with the Cisco WCS are available now in AirMagnet
Survey PRO and AirMagnet Planner versions 8.1 and work with Cisco WCS version
7.0 MR1 available shortly from Cisco
The
impact of smartphones and tablets on enterprise wireless networks
Author - Chia-Chee Kuan, CTO at AirMagnet / Fluke Networks
Smart
devices (smartphones, tablets, etc.) are proliferating and entering the
enterprise work place at a staggering rate. According to a Barclays Capital CIO
Survey 2011, the adoption medium is already very high for tablets, with 32+% of
organizations already supporting their use, and 35+% currently testing or in
trials. The functional differences between conventional PCs and smart devices,
like tablets, is getting smaller too. Data suggests that these devices will
replace 45% of notebooks and 12% of desktop PCs. Because of these smart devices
advances, the wireless LAN (WLAN) rose to become the #1 priority for enterprise
networking in 2011 (from #2 in 2010).
This
shift is not surprising. Wi-Fi is an off-load option to cellular carriers and
customers. When possible in the work environment, many users piggyback onto the
corporate network with their devices. With 3G and 4G data usage and device
adoption exploding (along with the cost), the data suggests the corporate WLAN
will continue to be flooded by new devices and heavy bandwidth consumption.
According to Cisco Visual Networking, 55-70% of all indoor mobile data traffic
happens over an indoor wireless network. Enterprise Wi-Fi and the WLAN is
quickly becoming THE access option for mobile users. It not only offers higher
bandwidth, but also delivers it at a lower cost and can fill in the voids where
3G/4G might not be available. With the capability gap closing quickly between
smartphones and tablets, users may be less inclined to use their laptops and PCs
(especially if their job requires them to be highly mobile).
With
all these smart devices hitting the enterprise, what impact does it have to the
Wi-Fi network? The most obvious is the increase in bandwidth demands and a need
to expand the WLAN to include more coverage area. However, it also creates a
management nightmare with client devices blurring the lines between rogue device
or legitimate communication tool. These lines can be further blurred with
tethering and rogue access points. Furthermore, new Wi-Fi attack tools
specifically designed to work with smartphones and tablets pose further risk
(and they're being published online). It's not unusual to see someone in your
building walking around with a smartphone or tablet. And that's the problem,
that same inconspicuous person could be attempting to execute an attack on the
network. A good example of this type of security flaw is the recent Android
vulnerability, which leaves the majority of Android smartphone users (running
Eclair, FroYo and older Android versions) susceptible to a type of attack called
Sidejacking when connected over unencrypted Wi-Fi networks.
While
the dramatic increase in smart devices certainly complicates the security,
performance and ongoing management of a WLAN, a robust wireless intrusion
prevention system (WIPS) can help monitor and manage the wireless airwaves
(hyperlink to AME webpage). These types of centralized systems proactively
protect Wi-Fi networks and users from all types of threats, even those
unintentionally brought to work on a smartphone or tablet. As these new devices
come to market, don't ignore their impact. Embrace the potential they offer the
enterprise, and proactively work to secure and manage them so they become less
of a risk and more of an asset.
AirMagnet Enterprise 9.0 Innovation Redefines Wireless Network Protection
EVERETT, Washington Fluke Networks today announced the availability of AirMagnet Enterprise, Version 9.0, the industry's premier wireless intrusion prevention system for managing and securing corporate WLAN deployments. The latest release introduces dynamic threat protection technology for WLAN security and performance management that eliminates Wi-Fi downtime and disruption by allowing organizations to dynamically update and defend the corporate network when new threats emerge.
This type of automated technology, referred to as dynamic threat updates (DTU) in AirMagnet Enterprise 9.0, is not available in any other WLAN security product. Until today, this type of protection has only been available in wired security products. Current wireless security offerings require that users schedule downtime to upgrade the firmware of the entire WLAN network in order to get protection updates. Not only is this process disruptive, but typically delays the update process for months, leaving organizations unprotected from the latest threats.
"AirMagnet Enterprise 9.0 takes WLAN threat protection to a whole new level with the introduction of DTU and represents a significant breakthrough for our market. No other independent or integrated WIPS platform supports such an automated process with immediate deployment and threat database update capabilities," said Chia-Chee Kuan, VP of engineering for AirMagnet products at Fluke Networks. "This innovation makes it possible to instantly create and seamlessly disseminate threat updates to the global AirMagnet Enterprise customer base - a first for wireless security."
AirMagnet Enterprise 9.0 now offers the only comprehensive, real-time approach to threat analysis and updating. It delivers a simple, scalable WLAN security monitoring solution that enables any organization to proactively mitigate all types of wireless security threats, enforce enterprise policies, prevent wireless performance problems and audit the regulatory compliance of all their Wi-Fi assets and users worldwide. AirMagnet Enterprise provides complete visibility and control over the wireless airspace, enabling any enterprise to reliably deliver the same standards of security performance and compliance for their wireless networks as they expect from their wired networks.
Similar to mature network IDS and AV products, AirMagnet Enterprise 9.0 supports automated on-demand updating of the threat signatures that define the security and performance detection mechanisms on a WLAN, guaranteeing the highest protection against newly discovered vulnerabilities. This rapid threat response brings a new level of protection to the WIPS marketplace and helps AirMagnet further alleviate the management burden placed on IT staff and resources.
This innovation is made possible by a completely new, extensible security event detection definition engine that enables rapid development and modification of new threat detection signatures. These can be instantly created and made available to the global AirMagnet Enterprise customer base. Furthermore, AirMagnet Enterprise's policy signature database is now separately loadable and no longer embedded in the server software. This new internal architecture also enables the future support for tools that will allow users to create their own signatures in real-time and share them with the community. Furthermore, DTU allows zero-day protection from new threats via immediate and automatic installation of new signatures when available.
"Customers feel unprotected from new vulnerabilities when waiting months for software updates to their WIDS or AP system. Security teams need quick and simple methods to update threat databases when new vulnerabilities are discovered and signatures developed. The new DTU capabilities in AirMagnet Enterprise 9.0 make this a reality," said Kuan.
Other Enhancements in AirMagnet Enterprise 9.0
New AirMagnet Spectrum XT Allows
Custom Signatures For WLAN RF Interference Issues
Author - Chris Roeckl, vice president of marketing at AirMagnet
Calling all wireless professionals! AirMagnet is releasing the latest version of the industry's first USB-based professional spectrum analyzer solution, AirMagnet Spectrum XT 2.0.1. What's new?
With this release, AirMagnet allows customers to create custom signatures for any RF (radio frequency) interference issue or source in the wireless LAN (WLAN) spectrum, regardless of device or environment. In addition, AirMagnet Spectrum XT also delivers the industry's most comprehensive RF interferer classification library and new custom technology to detect and classify any RF interference source, allowing customers to quickly identify and fix problems. Wireless professionals no longer have to depend on spectrum analyzer vendors to deliver database updates for detection of new devices.
Dilip Advani, the Spectrum XT product manager at AirMagnet said, "A common pain point for wireless managers and administrators has been the ability to classify and create a custom signature for a recurring problem unique to a specific network environment or architecture. AirMagnet Spectrum XT meets this demand and provides a more-efficient method for troubleshooting RF interference issues, saving time and costly IT resources."
AirMagnet Spectrum XT now boasts the largest RF interferer signature database and library for mobile spectrum analyzers. This includes new detections for radars, zigbee devices, motion detectors, RF signal generators, non-Bluetooth wireless mouse and more. It also offers the ability to create custom signatures, dramatically enhancing RF troubleshooting capabilities. Customers now have the option to create signatures and share them across multiple locations. These signatures also get logged into the AirMagnet database. Users can prioritize custom signature creation by visualizing the impact on WLAN performance beforehand. They can also take advantage of FFT spectrum freeze and capture techniques for more accurate and better spectrum analysis.
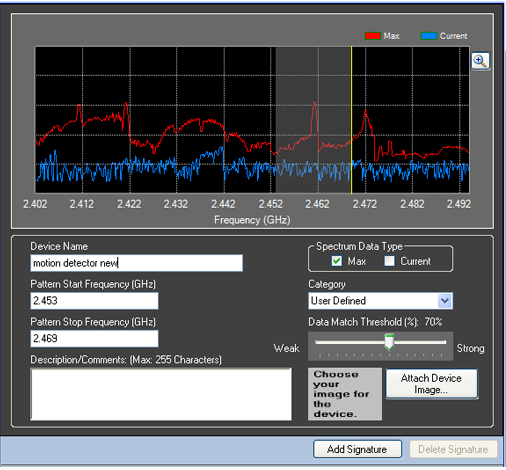
Why is this important? Let's look at a quick example. If a healthcare institution has a medical device that causes problems in their network environment, the organization can create a new signature on the fly and very quickly classify those types of devices. They can share that signature with other branches of the institution, if they have a similar device in their environment that is causing problems. These new capabilities in AirMagnet Spectrum XT eliminate the need for the healthcare company to depend on a spectrum analyzer vendor to create a signature and add it to the default classification database (which can take months and in some cases years). That has a huge impact on the time and cost it takes to troubleshoot RF issues.
Finally, the new release has a few other additions, including:
Great Information Shared in the Latest Network World Wi-Fi Challenge
Author - Jesse
Frankel at AirMagnet
I recently had the pleasure of recording a podcast for the Network World Wi-Fi Challenge with analysts Robin Layland and Joanie Wexler, as well as Manju Mahishi, director of wireless product strategy at Motorola Solutions. During the session, we covered a wide variety of WLAN topics, from best practices for reliability to dealing with latency, client devices and more. You can listen to the full recording here: http://solutioncenters.networkworld.com/wifi_challenge/registration/7229.html?source=nwwzne, but I'd like to also share with you some of the highlights from the conversation.
When asked about best practices and special tools needed to keep video performance at a high quality and reliable in a Wi-Fi environment, there are basically three things that need to be in place to build a robust network:
We also discussed must-have RF monitoring or management tools that an enterprise running mission critical WLAN application should have. We came up with a pretty comprehensive list of must-haves, including:
We also got into the topic of overlay tools vs. integrated tools. You can listen to our full responses towards the end of the podcast, but here's a little snippet:
"We (AirMagnet) take the approach that the access point has an important job to do, and vendors like Motorola have a lot of expertise in putting together that traffic-moving function in the AP, but we focus purely on the measurement, monitoring and analysis function of the information traveling through the AP. Because of this, we're able to take full advantage of all the capabilities of that device, purely dedicated to that set of features, which results in what we feel is a better, dedicated approach to security and performance management. "
Identifying WLAN Interference
Author - Dilip Advani,
Product Marketing Manager at AirMagnet
Performance is key when deploying a business-critical WLAN. However, with technology evolving so fast in the workplace, keeping a WLAN operating at a high level can be extremely challenging. Whether it's network connection issues, bad download/upload speeds, poor application performance or mobility issues, identifying sources of WLAN interference is vital to success.
When deployed properly WLANs deliver an exceptional networking platform that can dramatically boost productivity and corporate efficiency. Unfortunately, many networks are not deployed properly, are not configured correctly, have multiple sources interfering with the network, suffer internal and external security attacks and lack the monitoring and maintenance required for a healthy deployment.
Today, we'd like to talk a little bit about best practices for diagnosing WLAN interference.
First, what is interference? In the WLAN world, interference is a wireless radio signal that occurs on the same frequency as your wireless network, at the same time. Some of the key influencing factors are strength of signal, how often the signal is present (duty cycle), and variety of frequencies that are impacted. It's important to note that inference sources on a WLAN can be difficult to recognize until they impact performance. This impact is more visible in bandwidth-sensitive applications than data-only apps.
What or who causes the interference in a WLAN? The biggest culprits are WLAN devices (co-channel or adjacent channel interference) and non-WLAN sources. (When investigating interference, it's recommended that staff rule out Layer 1 interference before investigating into higher layers.) Either way, many of these sources are "invisible" threats or RF emitting sources that are present in every corporate environment, inside most devices or equipment.
Let's look at some of the non-WLAN sources of interference, since most WLAN sources are well-known:
Bluetooth can be a big source of WLAN interference. It operates in the 2.4 GHz spectrum and is commonly built into computers, cell phones, headsets, keyboards, mouses, printers, medical equipment and more. Research indicates that bluetooth devices have tripled in use from 600 to 1800 million units from 2006-2012. How do you avoid some of these interference issues from Bluetooth?
Start by changing your WLAN from 802.11b/g (2.4 GHz) to 802.11a (5 GHz). Next upgrade to the 802.11n standard and set it up to run in the 5 GHz channels or frequencies. Then use Bluetooth devices that are based on the version 1.2 specification or later, which uses Adaptive Frequency Hopping (AFH).
Microwave ovens are another bad source of WLAN interference and significantly impact performance. They typically operate around channel 9 in the 2.4 GHz spectrum, with a 50% duty cycle. All the ovens emit a strong and dirty signal over the entire 2.4 GHz band. A recent study found that microwave ovens operating within 10 feet of an 802.11b/g access point could significantly impact WLAN performance,with up to a 75% drop in network throughput.

To avoid this network impact, avoid using 802.11b/g technologies near a microwave. Make sure to keep a "safe" (at least 10 feet) distance from ovens and find out the center frequency of the model and steer your WLAN away from it. Finally change your WLAN from 2.4 GHz to 11a or 11n (5 GHz).
Radars and Lighting Fixtures can also interfere with WLANs. For example, fluorescent bulbs emit 2.4 GHz frequency radio waves. Cordless phones, available in 2.4 or 5 GHZ models, and motion detectors with sensors operating in the 2.4 GHZ spectrum, also impact performance. For cordless phones, don't waste your time switching AP channels (the RF signal spreads over all channels and frequencies), try to use phones operating in different spectrums, or implement those using Digital Spread Spectrum technology. Also, maximize the distance between APs and cordless phone bases.
Wireless security cameras, wireless game controllers and baby monitors also impact performance. For cameras, deploy brands that operate in a different spectrum from Wi-Fi and check operating channels to avoid overlap. For game controllers, check operating channels to avoid overlap and place the controller and wireless router as far apart as possible. With baby monitors, check operating channels and avoid overlap, buy brands that operate in different spectrums and place the monitor far from the wireless router.
Also be aware of the emerging Zigbee devices (which operate in the 2.4 GHz spectrum). They are common in lighting controls, HVAC, heating, smoke detectors, patient monitoring, asset management and more. They're expected to grow in adoption 68% from 2009-2012. Furthermore, be aware that some sources of interference are intentional, such as RF Jammers, and pose a significant security risk (like bridged networking technologies, client access devices and more).
The information above is just a sample of non-WLAN sources that can impact network performance. Here are some basic steps for solving interference problems:
* If yes, what policies can be put in place in the future to avoid the same mistake. If no, make WLAN changes to work around it.
To navigate the basic steps, we highly recommend you use an RF Spectrum Analyzer. This will help you detect and analyze signals in a range of frequencies, and provide true and accurate device classification. It can be extremely helpful for network technicians, engineers, administrators, installers, integrators, auditors and others. Most on the market are portable, lightweight and easy to use
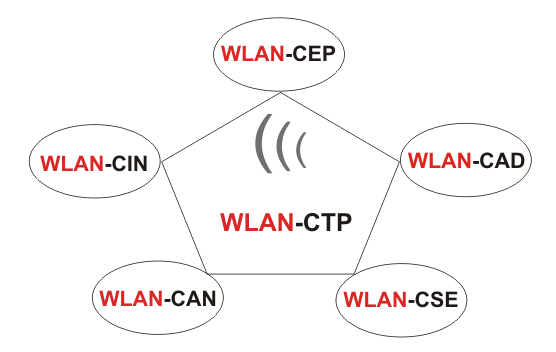
Wireless LAN Certified Training Program (WLAN-CTP)
www.wlan-ctp.de, www.wlan-ctp.eu, www.wlan-ctp.com, www.airdefense.de, www.cnti.de